What recent tech fads has your SMB dismissed as silly? 3D printing, internet of things…Pokémon GO? Juvenile as they may seem, these trends helped a lot of businesses make money. Navigating them may seem like a lost cause, but with the right know-how, you can earn profits by exploiting current tech trends.
Cash in on tech trends with these 5 tips
Android phones at risk of Malware
What is Virtualization as a DR solution?
Watch out for this persuasive phishing email

Anglers catch fish by dangling bait in front of their victims, and hackers use the same strategy to trick your employees. There’s a new phishing scam making the rounds and the digital bait is almost impossible to distinguish from the real thing. Here are the three things to watch out for in Office 365 scams.
Customize your Windows 10 experience
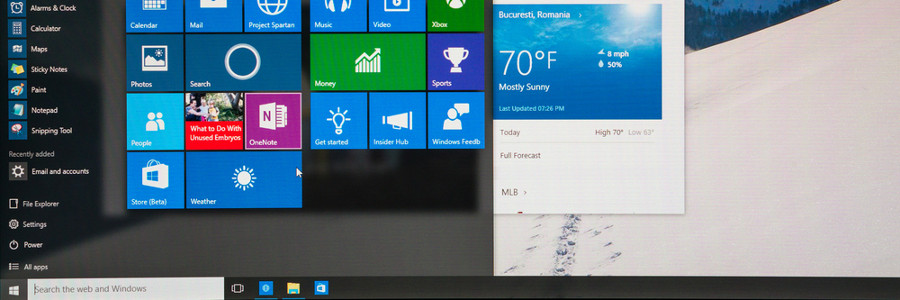
You log into your PC and you’re greeted by an incredibly plain desktop background and an equally drab Start Menu. Suddenly, a notification goes off and tells you that an application you barely use is ready for an update. Sounds like a nightmare, doesn’t it? If you want your desktop to look or behave a certain way, try out these tips to personalize your Windows 10 experience.
6 tips to install the newest iOS update
Can AI enhance your e-commerce business?

Artificial intelligence (AI) or “machine learning” has quickly transformed from science fiction to reality, and is currently on track to become an integral part of the corporate business environment. According to experts, by 2020 85% of all customer interactions with businesses will occur via machine learning programs.
How business continuity plans can fail
Find cool uses for your old Android tablet
Ways to handle virtualization security risks

Online blogs and forums mostly cover networks and the cloud when it comes to cybersecurity, leaving other types of technology -- particularly virtualization -- overlooked and unsecured. If you don’t have the right defense plans in place, your business will be vulnerable to all types of cyberthreats.
- 1
- 2